Killer applications for Blockchains thus far
Blockchains, and cryptocurrencies by extension, have captured the imagination of almost everyone. Hardly a day goes by without Bitcoin being mentioned in the news.
By and large, most things in this industry are based in speculation, but if you look abit further out and abit deeper in, you will see the seeds of something incredible happening before our very eyes!
In this short article, I highlight some of the “killer products” for blockchains, beyond the speculative trading of Bitcoin. Coincidentally enough, some of these use-cases fly in the face of Bitcoin maximalists who posit that blockchains are only good as money and shouldn’t be used for anything else - the derision from this group of maximalists is always “you might as well use AWS for X,Y,Z“, but as you will see, using AWS for some of these functionalities misses some of the unique cryptographic properties offered by blockchains.
Here are, in my opinion, some of the main themes and killer products/applications of blockchains thus far:
1. Non-state issued Money (Bitcoin, stablecoins)
First breakthrough product for blockchains was money (Bitcoin). To be more specific, non-state sponsored money.
Bitcoin has gone on to evolve as a store of value, and another blockchain-based money product has taken over - stablecoins. Predominantly built on the Ethereum blockchains, stablecoin issuers have expanded to other blockchains such as Tron, Solana, etc.
These privately created monies, pegged to Fiat currencies, have blossomed and become the life-blood of the crypto markets.
The BIS (Bank for International Settlements), a kinda central bank for central banks, even posited that these stablecoins can co-exist with CBDCs (central bank digital currencies).
Make no mistake - Bitcoin, and by extension stablecoins, have pushed the digitization of banks faster than anything.
Akin to how Tesla pushed the electrification of vehicles- at first they laughed, then scorned and now every car company is suddenly speaking as experts, as if they always knew and had plans for electrification - utter nonsense! The same is the case with digitization - COVID may have been the fuel, but Bitcoin, and broader crypto ecosystem, was/is the fire!
2. Fundraising (ICO, IEO, IDO)
A second breakthrough product for blockchains was fundraising mechanisms which became all the craze in 2017. This became an alternative to IPOs for companies to raise money from the public and an extension of crowdfunding, for projects to raise money.
EOSIO blockchain developer Block.One raised over $4 billion in their year-long ICO. There have since been variations of the ICO model, namely:
ICO - initial coin offering
IEO - initial exchange offering
IDO - initial dex offering
The raises range from hundreds of thousands of dollars to hundreds of millions. It’s crowdfunding on epic proportions.
3. Provable ownership of digital goods (NFT)
Another killer product for blockchains emerged during the same phase as the fundraising - provable ownership via means of games like cryptokitties.
NFTs have grown to be a wildly popular killer product for blockchains, especially in 2021. Cryptographically provable ownership of digital goods (art, games & items) will continue to grow in popularity, outside the niche crypto ecosystem. We have seen art auction houses such as Sothebys list NFT art that gets sold for millions.
Outside of the niche crypto ecosystem, NFTs are by far the biggest killer product. Dapper Labs, the company behind Cryptokitties, which also created the NFT standard on Ethereum, also have an NFT based platform that is huge outside of crypto - NBATopShot, among others. They create officially licensed digital collectibles, which have become absolute hits among sports fans and stars alike. Dapper have also created their own blockchain - Flow.
Patents as NTFs is the next logical extension of this. Music, art and many more - all digital content that could be on chain, will be on-chain.
4. Decentralized Financial Services (Defi)
While Bitcoin & stablecoins, as money, was the killer use case for blockchains, it wasn’t until circa 2020 when Ethereum-based Defi came along that another killer product was realized - financial services such as lending, borrowing, market making, etc - some key primitives.
Defi, while for the most part currently speculative, has painted a picture of the world to come - financial services without the middle man, relying on smart contracts. A digital wallet essentially becomes your bank - akin to what Mpesa and others around the world have already done. This continues to be a huge deal.
Products such as Compound and Aave have ballooned to be massive borrow/lending protocols utilizing billions of dollars.
Dexes (decentralized exchanges) also became huge, as of the financial services primitives allowing for listing & market marking for almost anything imaginable. Uniswap is big (within crypto) and there have been many more Dexes doing incredible volume, listing fantastic stuff.
5. Advancements of privacy technologies
This may sound like a stretch here, but bear with me while I make this case : privacy, via cryptographic means, has been brought to the fore with blockchains. Zcash and Monero are the two most-known blockchains that offer real privacy when transacting. They use different cryptographic primitives such as Confidential transactions, pedersen commitments, bulletproofs and zero knowledge proofs (ZKP), and others.
As already covered in my previous post, zero knowledge proofs were mostly theoretical for close to 30-40 years, up until blockchains arrived and not only implemented but also advanced this field of ZKPs. I would recommend you read through that earlier post to see how much bigger the applications of ZKPs are - from currencies, to cybersecurity and verifiable identities.
I firmly believe ZKPs haven’t come onto their own yet, but will be a big part of daily interactions in the future. They will be a big deal.
Zero Knowledge Proofs - an overview (without the maths)
If you spend enough time in the cryptocurrency/digital assets space, you will hear the words “Zero Knowledge” mentioned quiet often. For most, the maths just block out all the maths and cryptography terminology when people talk about zero knowledge proofs.
In this short post, I will attempt to explain zero knowledge proofs as well as their many applications - all without the hard maths and cryptography formulae.
Zero Knowledge proofs isn’t new, it’s been around since the 1980s - although mostly theoretical, in recent years this field of study has taken a life of its own with the practical implementation in the blockchain space.
Cool, but what are Zero Knowledge proofs (zkp)?
It’s a protocol used for mathematically proving knowledge of something by one party (“Prover”) to another party (“Verifier”), in such a way that the proof doesn’t leak any more information.
Every Zero Knowledge proof contains the following properties:
Completeness - if the proof is true, the Prover can prove it repeatedly
Soundness - if the proof is false, it’s very hard for a Prover to claim it’s true to the Verifier
Zero Knowledge - if the proof is true, no other info about it is disclosed to the Verifier
In other words, one can prove knowledge of something, without disclosing that ‘something’ or providing clues that could lead to the knowledge of that ‘thing’, but done in such a way that the party you are proving to is satisfied of your knowledge of that ‘thing’. These Zero Knowledge proofs prove knowledge of something, not merely its existence i.e. with zkp, I can prove my age, not necessarily prove that age exists. This blogpost provides some illustrations of such examples, but for a more deeper dive into zkps, this matter Labs Awesome Zero Knowledge Proofs repo contains alot of information.
Given the number of years this field of study has had, we can be assured that the maths/cryptography is correct. With this assurance, we can forgo trying to fully understand the maths/cryptography and focus, instead, on the various applications and implementations of this novel cryptographic field of study.
An overview of some major/well-known ZKP systems include zk-STARK, zk-SNARK and bulletproofs (efficient range proofs):
zk-SNARK is an acronym for Zero-Knowledge Succinct Non-Interactive Argument of Knowledge. This has the following explanation:
Zero-knowledge: if the statement is true, a verifier does not learn anything beyond the fact that the statement is true.
Succinct: The size of the proof needs to be small enough to be verified in a few milliseconds.
Non-Interactive: Only one set of information is sent to the verifier for verification, therefore there is no back and forth communication between the prover and verifier.
ARgument: A computationally sound proof: soundness holds against a prover that leverages polynomial-time, i.e. bounded computation.
of Knowledge: The proof cannot be constructed without access to the witness (the private input needed to prove the statement)
zk-STARK is an acronym for Zero-Knowledge Scalable Transparent ARguments of Knowledge. zk-STARKs improve on the scalability of zk-SNARKs, but also removes the “trusted setup” which zk-SNARKs rely on. Trusted setup is the process of requiring a trust third-party to initially setup the ZK proof system. But this reliance on a third-party weakens the privacy properties of such a system. What zk-STARKs rely on instead, is to use publicly verifiable randomness to create trust-less, verifiable computation systems.
Bulletproofs are short non-interactive zero-knowledge proofs that require no trusted setup. Bulletproofs are a new type of more efficient range proofs (a range proof is basically cryptographic proof that a secret number is within a certain range e.g. with range proofs, I can prove that my age is between 19 and 25 years old, without expressly disclosing my age - just the range)
These ZKPs all differ with sizes of proofs, time it takes for proof computation, etc. These zkp implementations in blockchain protocols help with financial privacy, security size and speed of the values transacted on these protocols.
ZKPs in Blockchains
Ethereum, Zcash, Grin, Monero, Beam, Mina & Aleo, etc are just a few of the many blockchain protocols that utilize some form of ZKP.
Since there is already ample content about ZKPs in the blockchain ecosystem, we won’t dwell much on this application/implementation.
ZKPs in CyberSecurity
Vulnerability/exploit disclosures
An interesting development of ZKPs in CyberSecurity field is one spearheaded by DARPA (Defense Advanced Research Projects Agency) as part of their Securing Information for Encrypted Verification and Evaluation (SIEVE) program. Specifically, the focus is using ZKPs in vulnerability disclosures, such that a researcher can prove to a vendor that, not only does a particular vulnerability exists but that they have an exploit for such a vulnerability, all the while without revealing any further details about the vulnerability or exploit in question.
2 teams that took part in this DARPA challenge, Galois and Trail of Bits have already developed capability to mathematically prove exploitability of vulnerable software without revealing critical information. Trail of Bits have a more detailed walk-through of their thought process on this. Galois also have an overview of their approach to this in their Project Fromager.
Authentication (e.g username, password, MFA)
M-Pin is client-server protocol, which features two-factor client authentication as an alternative to Username/Password.
The basic idea is that a registered client is provided with a cryptographic secret, which is used to prove to a server for authentication purposes; all without ever disclosing the secret to the server. This means no information about that secret is ever stored on that server.
The cryptographic key is split into two factors for authentication : a user-select PIN and a token (stored in the Browser, for example). I recommend reading the paper linked above about this protocol.
There is already a live product that uses the M-Pin protocol, MIRACL Trust®, a cloud-based MFA platform that provides secure, multi-factor authentication to employees, partners, and external users without sending authentication credentials across the web for storage in the cloud.
Cyber Attribution?
The U.S Intelligence and Law Enforcement agencies have been public about some attributions, without always being in a position to disclose how knowledge of that information came about - it could be via sources, via compromising enemy infrastructure, etc. So it’s understandable why it would not be operationally wise to disclose that information.
We are required to trust and believe the unnamed methods and sources from these agencies relating to their attribution.
Although unsure of how the actual mechanics would work, on a theoretical level, this is another area which zero knowledge proofs would be beneficial for cyber attribution. Just as with how they have always done it, they could make a statement, and prove they have this knowledge, in such a manner that the public, and indeed the outed enemy, wouldn’t know exactly how they know, but would be assured that indeed that knowledge and proof is true.
We can leave it up to DARPA to fund another program to tackle this :-)
ZKPs in Decentralized Identity Standards
Microsoft and the Decentralized Identity Foundation, among others, have an initiative for Zero-Knowledge Proof scheme that enhances user privacy and security for digital credential systems.
Current issues with Verifiable Credentials (VCs), which their SNARK-based ZKP credential scheme could address
The specific scenarios their zk-vc scheme is looking at are: Publishing a resume on a career networking app, checking the current status of work history credentials or interviewing for a new job.
I would highly recommend you read their paper, zero knowledge credentials with deferred revocation checks, on this if this is of interest to you.
Conclusion
Many of us, being non-cryptographers or mathematicians by training, tend to shut off our minds when reading/hearing about most things cryptography related (we only like the cryptocurrencies coz….hey, who doesn’t like money :-D ).
But I hope this short post has given you an overview of the various applications of zero knowledge proofs beyond just blockchains.
How Eth2.0 mitigates specific PoS (Proof of Stake) attacks
In December 2020, ETH2.0 Beacon Chain launched. This Phase 0 launched forms part of a multi-year process that will see ETH1.x transform from a PoW (Proof of Work) to a PoS (Proof of Stake) blockchain.
This is an exciting period in Ethland and is the product of years of research of optimal solutions to ensure Ethereum remains secure and decentralized despite a change of consensus mechanism. its been a long held belief that PoW has the most security guarantees unlike, say, PoS.
I have previously covered some forms of attacks against Proof of Stake chains and so, with Ethereum moving to PoS, let’s see how it intends to defend against these PoS attacks or if any are applicable at all!
Nothing at stake attack - This attack relies on the assumption of "cheap" (almost nothing) mining on forks of the same PoS (Proof of Stake) chain. Multiple forks couldn’t be detected or discouraged.
Long range attacks - this attack occurs when an adversary creates a branch/fork on the blockchain starting from the Genesis block (or thousands of blocks in the past) and overtakes the main chain, thus rewriting history.
Eth2.0’s security model is making attacks extremely expensive by putting up economic value-at-loss i.e. security relies of penalties, not rewards.
Eth2.0:
solves 1) (nothing at stake) by making use of a punitive proof of stake algorithm where validator rewards are withheld if they sign blocks on competing forks. This was called Slasher and introduced by Vitalik in 2014.
We have indeed already seen a validator get slashed ~0.25 ETH:
An ETH2.0 validator slashed due to a violation
solves 2) (long range attacks) by accepting “weak subjectivity”, which is one of the root causes of long range attacks. Weak subjectivity relates to new nodes and offline nodes that come online after a significant amount of time. These nodes would not be able to immediately distinguish which of the branches it received is the main chain. With Proof of Work, it's easy to determine the main chain as it is the one with the most proof of work, whereas in Proof of Steak, since there is no 'work' done, it's easier for such nodes to be deceived, at least for a time.
Eth2.0 Beacon Chain uses weak subjectivity checkpoints, which is a similar concept to “genesis block”, in that it’s a block that is agreed upon by the entire network as the “real” chain.
The Eth2.0 research work went a step further to determine a weak subjectivity period - which is defined as the number of recent epochs within which there must be a weak subjectivity checkpoint so that an attacker who takes control of the validator set at the beginning of the period is slashed at least a threshold amount in case a conflicting finalized checkpoint is produced.
The Ethereum re-engineering from PoW to PoS has been defined as "trying to change an airplane engine mid-flight”. It could be disastrous if it all goes wrong, but so far, all the research work and planning that went into this is moving along nicely.
I will be eagerly watching, and researching, this progress over the next 12-18 months!
The impact of community currencies in low-income communities
Let a thousand currencies bloom - Bernard Lietaer
In 2012, I was part of a Youth Innovation Showcase where I presented an idea of a platform called Commune. One of the 3 focus areas of the platform was on stimulating local economies via cash mobs:
Excerpt of my pitch at a 2012 Youth Innovation Showcase
Needless to say, that idea and platform didn’t have an opportunity to fully materialize as I had hoped. I was bitten by the Cyber Security bug and developed new interests.
Since then, one idea had unexpectedly captured my attention - community currencies. Till then, I had only known the 180 world currencies as recognized by the United Nations.
But reading the works of Bernard Lietaer and others like Thomas H. Greco spoke volumes on this. I particularly liked Lietaers’ focus on local economic development with these complementary community currencies.
These “slum economies” or community currencies are complementary mediums of exchange to a national currency and serve a particular purpose - stimulating local economies during times of business downturns and help provide for basic needs when the national currency is in short supply.
In his 2001 paper, The Economics of Community Currencies: A Theoretical Perspective, Shraven sates: “when the national money fails to facilitate all potential exchanges of a sub-set of the economy that has strong economic interconnections, a complementary currency can alleviate this problem”
By then, I was already aware of Bitcoin, but it wasn’t until much later that I began to think of Bitcoin as a form of community currency (more on this in a follow up article).
In The Future of Money, Lietaers provides a few examples of such complementary community currencies:
Time Dollars - invented by a prominent Washington lawyer and applied in several hundred communities in the US
Ithaca HOURS - a paper currency launched by a community activist in the small university town of Ithaca, New York. Ithaca is a relatively low-income community of about 27,000 inhabitants
Tlaloc - a popular Mexican neighborhood currency
Bia Kud Chum - the first South-East Asian community currency
WIR - an independent complementary currency system in Switzerland that serves businesses in hospitality, construction, manufacturing, retail and professional services.
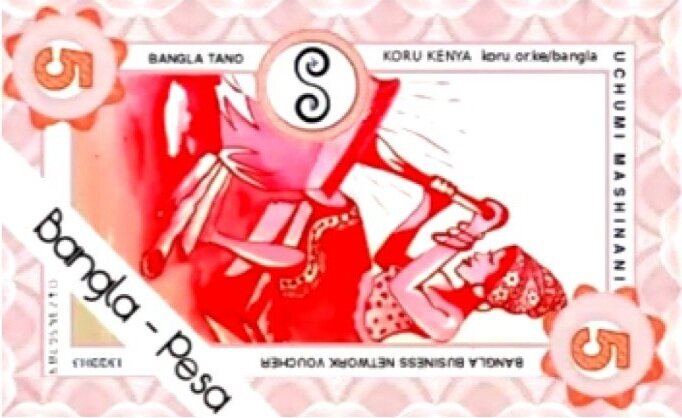
Closer to home, there is one few have heard of Bangla-Pesa - a colorful paper-based complementary community currency used in the slum of Bangladesh in Mombasa, Kenya. It is a voucher that traders and service providers use as a medium of exchange.
Bangla-Pesa community currency
Benefits of community currencies
There exists ample research on the impact of community currencies and how they contribute to sustainable livelihood in poor and informal settlements. It’s worth noting, however, that some community currencies like ithaca Hours, lack clear evidence of economic advantage.
But, some community currencies do show clear evidence of economic advantage.
Below are some examples of these economic benefits of community currencies like Bangla-Pesa:
Daily purchases in Eco-Pesa community currency allow members to save money in their national currency which they would have spent otherwise (these community currencies function as mediums of exchange and are not meant to be stores of value)
83% of business participants reportedly saw an increase in total sales, attributed to Bangla-Pesa
Members have a significantly higher food consumption than non-members, as well as a generally higher food budget
The Bangla-Pesa community currency accounted for 22% increase in monthly income
The Liquidity Problem & Blockchain Solution
There are, however, a few problems with community currencies :
Value generated within the community stays within the community. It cannot be spent within another community
Lack of trust
Scaling and design constraints (typically can’t scale beyond 100 - 200 businesses in the network)
These, among other issues, have been addressed to a degree by incorporating Distributed Ledger Technologies.
A recent paper on this issue stated: of the over 4,000 complementary currencies that have sprung up in 50 countries, most complementary currencies fail to create sustainable monetary alternatives due to low liquidity.
Liquidity is defined as the probability that an asset can be converted into an expected amount of value within an expected amount of time.
Blockchains can provide transparency, audit-ability and liquidity reserves with built-in convertibility between community currencies and promote greater usage and collaboration between communities. Users are empowered to exchange the community currencies for goods and services outside of the originating community as well as between national currencies.
A case in point is the Sarafu Network. Sarafu is a digital community currency and can be used akin to M-Pesa - the renowned Safaricom product.
Sarafu network dashboard
Documentation of the Sarafu Network can be found on their public Gitlab where they cover technical details such as their Smart Contracts, Blockchain choice (POA, xDAI), Wallets, Fiat on-ramps and off-ramps, etc.
Blockchain-based Community currencies
Grassroots Economics, an organization that spear-headed these community currencies in Africa, found that within a 6 months pilot of the Sarafu network:
4,065 Kenyans representing families living below the poverty line traded about $30,000 with each other
Linking 9 community currencies in circulation among 1,136 businesses, clinics and schools
2,567 daily farming wages had been paid
54,928 servings of vegetables
5,361 kilos of flour
2,506 rides on local transport
843 school tuition payments
484,404 liters of water
59 visits to the doctor
Mind-blown!
These aren’t just numbers, these represent healthcare, education, and sustenance for hundreds of families living below the poverty line, without depending on the government issued national currency.
Conclusion
I’m slightly saddened that during my work among marginalized communities years ago, I wasn’t aware of community currencies and focused on using national currencies. Maybe I could have done more. But i’m also over-joyed at the results I have seen over the years of tracking the impact of these community currencies.
Given the above data about the effects of community currencies, there is a case to be made for experimenting and deploying these in informal settlements around the globe. A few initiatives have already embarked on this journey and I hope we will see many more in the coming years.
I’m rooting for the success of all these projects!!
Archiving parts of my site on the Blockchain
The internet never forgets (until it has to)
I love blockchain technology in general. I’m an investor in, have written about, and am a user of, various blockchain platforms. I have also contributed by disclosing bugs in various blockchains.
I have used a few document storage blockchain projects like Storj, IPFS, etc a little under 4 years ago.
Now that I have my own site, I decided to look at these protocols again. I recalled a protocol that was on my radar called Arweave, a data storage blockchain protocol. I found it to be the easiest to use for what I wanted. I had read their whitepaper ages ago, but hadn’t really used their tech.
Today was the perfect opportunity to use it.
Arweave has a concept they call “permaweb”, built on top of the Arweave network.
The permaweb is a collection of interlinked documents and applications that get stored permanently on their protocol (so you may want to be careful what you put there).
I decided to put some sections of my site on the permaweb. Ironically, I opted to archive all the articles I wrote about blockchain technology - on the blockchain (technically “blockweave”)!
E.g. this paper - Future tourism trends: Utilizing non-fungible tokens to aid wildlife conservation is no longer pointing to the AJHTL Journal website. It is now pointing to, and archived on, the Arweave permaweb.
Archived paper: https://sqwgu2q52ul3lozh67aqok6l4sdqj4r455l2esuiktdt5xkfkb5q.arweave.net/lCxqah3VF7W7J_fBByvL5IcE8jzvV6JKiFTHPt1FUHs
View raw transaction : https://arweave.net/tx/lCxqah3VF7W7J_fBByvL5IcE8jzvV6JKiFTHPt1FUHs
View in block explorer: https://viewblock.io/arweave/tx/lCxqah3VF7W7J_fBByvL5IcE8jzvV6JKiFTHPt1FUHs
Why did I do it?
For fun. And because I like keeping my finger on the pulse of what’s happening in this industry.
In due time, I will migrate this entire site to be hosted, in parallel, on one of these blockchain protocols. Again, just for fun :-)
UPDATE:
I have pinned my 2017 article from Pentest Magazine on IPFS. The article is a tutorial on reverse engineering, exploit writing and micropatching - A new initiative of micropatching - 0patch!
This article on the impact of community currencies in low-income communities is also archived on the Arweave permaweb